When we put our sites on a new server last year, one Wordpress plug-in we retained, despite a known exploit, was Yuzo Related Posts. Basically, nothing else could do related posts as well. It just worked. Everything else, inexplicably, either did not do post relationships terribly well, was too resource-heavy, or was too ugly,
Fortunately, I ran Wordfence, who were among the folks who reported on Yuzo’s vulnerability in 2019. They believed their program would guard against it. In addition, I found some code on this page at Stack Overflow, and made those changes as well.
Maybe I got lucky as we didn’t get hacked, or maybe the above set-up helped, but with the latest Linux-based hack also using Yuzo (and many others), I decided to look again. I wasn’t going to tempt fate, and I do not recommend that you do.
Wordpress’s own directory has a lot of related-post plug-ins, but once again, I had to draw the same conclusion that I did in 2022. In fact, two of them didn’t even function! So much for them having been tested.
Yuzo, of course, was toast, having been removed from the directory.
But a further search revealed that Lenin Zapata, one of the two people behind the original, did indeed rewrite the plug-in completely, taking it from v. 5 to v. 6. The latest, last updated in 2020, was v. 6.2.2.
As far as I can tell, it’s a complete rewrite, but I am no expert on such matters. What I can tell you is the directory structure looks different. The bottom entry in the readme.txt is for the original, where Mr Zapata wrote, ‘Old version (with faults): A bad day’. The new one is ‘renewed and with maximum security’.
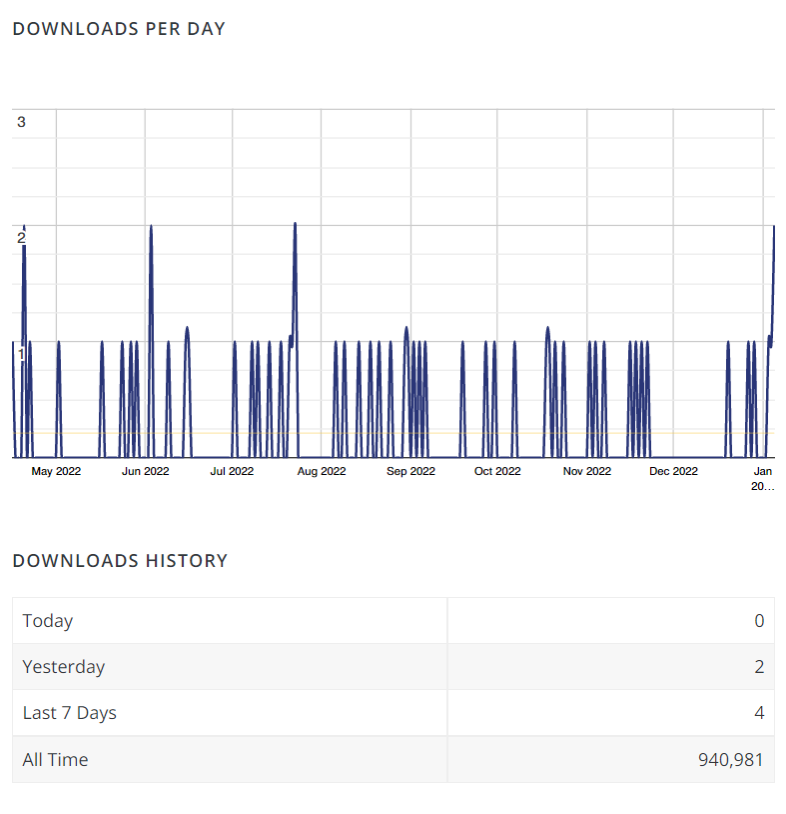
I am taking Mr Zapata’s word for it, but I was saddened to note that Wordpress has kicked even the new version off for a ‘Guideline Violation’. Strangely, my web history says I downloaded the latest one from wordpress.org, even though the site says it is ‘not available for download’. It must be in there somewhere and even Wordpress’s own stats said there were a handful of downloads over the last week.
No wonder he stopped developing it after both the disappointment of the exploit and seeing the plug-in get kicked off. Even if it was the best and, it seems, irreplaceable. I don’t know why no one has risen up to meet the quality of the original plug-in (the exploit aside), but maybe Lenin Zapata is just that much cleverer with figuring out how posts relate and with presenting PHP-generated content smartly. Have a look below—I think it looks very good and works very well.
I’m just hoping I’m doing the right thing by using a version that hasn’t reportedly fallen victim to the 2019 exploit. I don’t like someone getting a raw deal if they’ve fixed up something on which they made a mistake. They deserve a second chance.
Do I recommend you do what I did? No, because I don’t understand enough code to be able to report definitively that it was the right decision. But if you understand this stuff, have a peek at v. 6 and see if it does what it’s supposed to—safely. Or write your own to compete with it and do what so many of these plug-ins don’t or can’t.