One last post on this topic for now, since this entry is pertinent for a complete picture of what is happening with the Google malware bot.
Let’s just say for argument’s sake that I’m wrong, and the combined minds of the Google hive are right. An entire company of boffins must be smarter than a guy who doesn’t use automated teller machines, right? So, according to Google, our ad server linked to a location at bjskosherbaskets.com, which distributed malware on April 6. The difference is: we know our server’s been clean since April 6, and Google refuses to see this. Let’s buy into this fantasy and that we still link to this very dangerous, malware-distributing website via our ad server.
So what about this website at bjskosherbaskets.com itself? What does Google say about them?
You can try Googling for this site yourself, and you might see this:
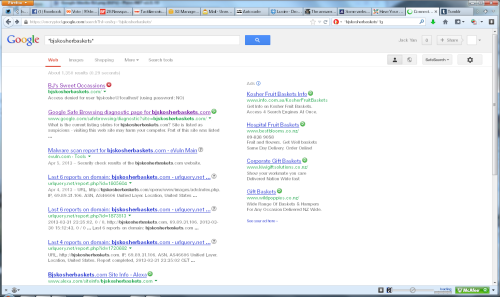
It exists, but McAfee SiteAdvisor (in my case) gives it a red X.
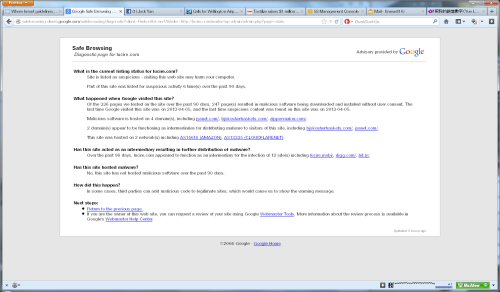
If you click through, you’ll get this advisory from Google:
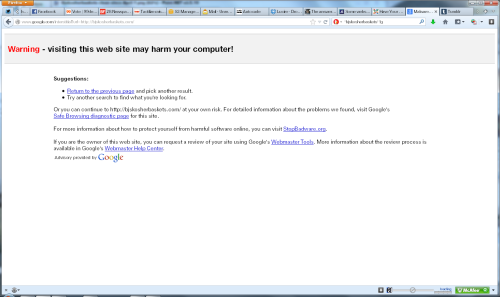
Oh dear, you mean it’s still infected? Tell me more, Google.
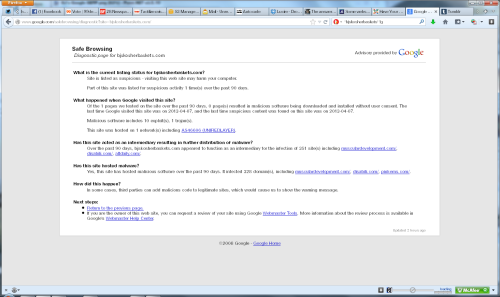
Um, nothing.
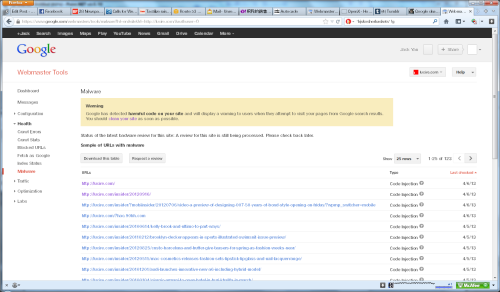
That’s right. Nothing is wrong with this website. It’s been clean since April 7. Yet Google still blocks this now-clean site and anyone who used to link to it. Even though we cleared the hack and don’t link to it any more, Google still insists that we do, and that we’re guilty for doing so. Even if we were still linking to it, and there’s nothing there that’s malicious, then too bad. I feel for the webmaster of this site, because they’ve done all they can—yet Google blocks them as well, 19 days after its own bot said it last picked up any issues.
The notion that Google takes five to seven hours to reclassify a site is clean is bollocks. This is running on nearly three weeks and Google is penalizing an innocent website. Even we don’t dare link all our sites back to our ad server, which actually harms the small businesses we feed through it. (Not to mention my own campaign ads! Though some of you might say that’s a good thing.)
I know we can turn off these advisories, but I doubt many will. I haven’t, because of FUD: what if I come across a site that really is infected?
The house of G continues to have the ’net by the short and curlies. And the sites that really are malware—Google’s Iphone hack via Doubleclick, for example—are clean according to the company, of course.
Since Google has spent 2013 targeting other ad networks (Netseer in one case, Isocket in another, and our ad server in the most recent case), could this be its online ad division trying to get a bigger slice of the pie? Accuse the competition of spreading malware, but always deem your own to be clean—even when it isn’t. Then it can try to dominate.
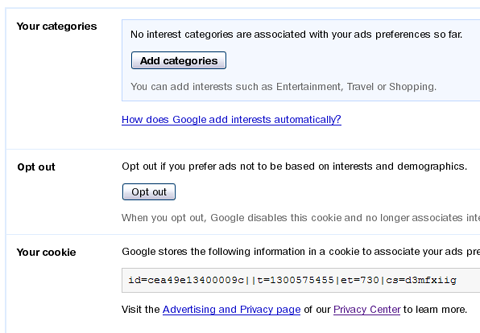
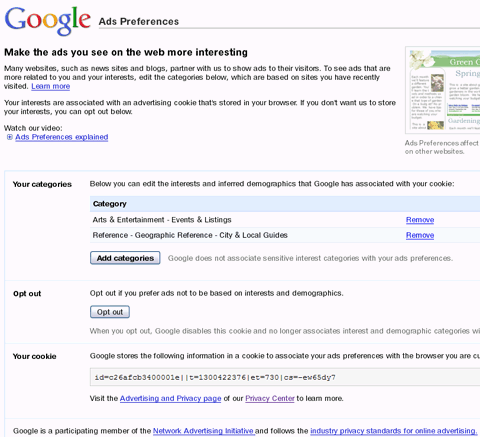
We already know it spied on users who opted out of advertising preferences, until it was busted by yours truly, and there was the spying on Iphone users last year that I mentioned above. It’s hard to put all this down to Google being a nice servant of the internet, when it took effort to program these spying mechanisms in. Having been busted on both, it’s desperate to continue growing its online advertising’s invasiveness. By accusing everyone else of malware—Isocket, for instance, is still puzzled by what caused it to be blacklisted along with “guilt by association” publishers who used its network—then online publishers might think Google’s the only game in town.
It isn’t, and I hope it never will be.



2 thoughts on “Someone has it worse: a site, clean since April 7, that Google still blocks”